![NIS-2 Umsetzung: Praxisleitfaden zur rechtssicheren Compliance [inkl. Checkliste]](/sites/hvs/files/styles/original_small/public/2025-12/praxisleitfaden_zur_rechtssicheren_compliance_inkl_checkliste_0.png.webp?itok=v90QnGKT)
Step by step to compliance
Step by step to compliance
![NIS-2 Umsetzung: Praxisleitfaden zur rechtssicheren Compliance [inkl. Checkliste]](/sites/hvs/files/styles/original_small/public/2025-12/praxisleitfaden_zur_rechtssicheren_compliance_inkl_checkliste_0.png.webp?itok=v90QnGKT)
The NIS2 Directive has been transposed into German law as of December 2025 and applies to approximately 29,000 organisations. For many companies, the key question is no longer whether they are affected, but how the requirements can be implemented efficiently and in a legally compliant manner.
This guide provides a step-by-step approach to achieving NIS2 compliance in practice – from scope assessment and determining your cybersecurity maturity level through a self-assessment, to a structured overview of all statutory NIS2 requirements, including a comprehensive compliance checklist.
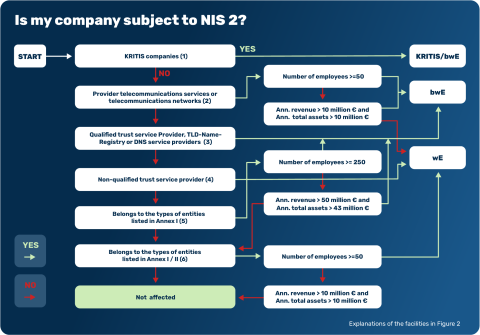
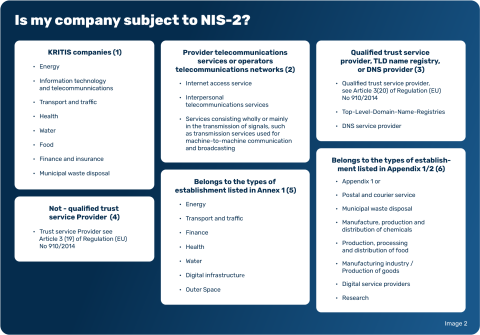
The classification under NIS2 depends on organisation size, revenue, and industry sector – however, the underlying criteria are complex. Using the HvS NIS2 scope assessment based on the graphic below, or the online tool from SKW Schwarz [German], you can quickly and systematically determine whether your organisation falls under the NIS2 Directive.
To efficiently determine the need for action regarding NIS2 compliance, a gap analysis is recommended.
Based on our experience, it is advisable to first check the extent to which existing ISMS documents – such as policies and process descriptions – already cover the requirements of NIS2.
Subsequently, the relevant business areas (e.g., IT, HR, procurement, and facility security) should be involved in the assessment of practical implementation through structured interviews and audits, in order to obtain a realistic picture of the current state.
An additional benefit of this approach is that the interviewees gain transparency regarding which areas should be prioritized when establishing the necessary processes and policies from the perspective of an auditor and consultant, thanks to the targeted questioning technique.
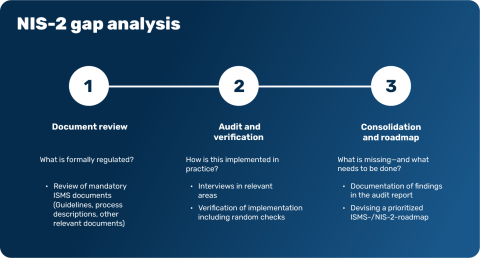
The identified deviations and gaps are documented in a report. Based on this, a concrete roadmap is developed, outlining which measures are necessary to achieve NIS2 compliance in a targeted and prioritized manner.
If you want to take the assessment of your current state into your own hands, we have developed a free self-assessment tool. The HvS NIS2 self-assessment tool provides a structured overview of how well organisations are already prepared for the requirements of the NIS2 Directive and in which areas specific action is needed.
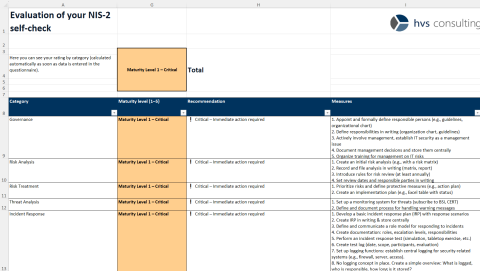
The tool systematically evaluates existing processes and measures against the statutory requirements and helps clearly identify implementation priorities and focus areas.
An information security management system (ISMS) forms the central foundation for NIS2 compliance. It establishes the organisational and structural prerequisites to systematically assess risks and effectively implement security measures.
Organisations that have already implemented an ISMS according to ISO/IEC 27001 or TISAX® can largely build directly on it.
For all others, NIS2 provides an appropriate opportunity to start introducing an ISMS in line with NIS2, thereby creating the basis for a sustainable and auditable implementation.
The NIS2 Directive (Art. 21) as well as the German NIS2UmsuCG (§ 30) define concrete requirements for affected organisations. The following points provide a concise overview of the minimum requirements that must be implemented to achieve NIS2 compliance:
Organisations are required to implement appropriate, effective, and proportionate risk management measures.
In practice, however, it is often observed that without a clear methodology, extensive risk registers with limited added value are quickly created. A focused, practical approach that prioritises risks and supports implementation is therefore crucial. Using a proven methodology, security risks can be evaluated in a structured manner and concrete, actionable measures derived.
Organisations need to establish appropriate processes for detecting, analysing, and managing security incidents.
Effective incident management defines clear responsibilities, escalation paths, and standardized procedures for handling security incidents, and forms the basis for compliance with the NIS2 reporting obligations.
How HvS Consulting can support you
If you do not have the required expertise in-house, the experts at HvS Consulting can provide professional support – for example, through our Incident Response Retainer or the HvS Threat Insights, which help organisations meet NIS2 requirements. Additionally, we offer an Incident Readiness Check (consultation), allowing you to assess in just one day where your organisation may need to improve its incident management capabilities.
Organisations must implement measures to maintain business operations during a crisis. This particularly includes backup and restore concepts as well as a structured crisis management approach, ensuring that the organisation remains operational in the event of serious security incidents.
Organisations must identify security-relevant suppliers and service providers and define appropriate security requirements. These requirements should be contractually anchored, and their implementation must be regularly reviewed.
Organisations must implement appropriate security measures for the development and operation of IT systems. This particularly includes structured patch and vulnerability management, effective malware protection, and the use of multi-factor authentication (MFA).
Organisations must regularly assess the effectiveness of their security measures. This includes, among other things, audits, the use of appropriate key performance indicators (KPIs), and technical assessments such as penetration tests.
Organisations must conduct regular awareness activities and training for employees and executive management.
Executive management plays a particularly important role, as it is responsible for the strategic direction and oversight of cybersecurity measures.
Organisations must use appropriate cryptographic methods according to the state of the art to effectively protect data and communication channels. This particularly includes the secure encryption of stored data as well as the protection of data transmission.
Organisations must implement appropriate access controls to ensure that only authorised personnel have access to systems, applications, and data. This particularly includes role-based access concepts and regular permission reviews.
In addition, security aspects must be integrated into personnel processes, for example during onboarding, role changes, and offboarding, to effectively prevent misuse and unauthorised access.
Regardless of the prescribed measures, the formal obligations must also be observed. This particularly includes timely registration and compliance with reporting obligations for security incidents. Further information can be found here:
In other words, implementing the NIS 2 requirements - or, more generally, the effort to strengthen an organization’s resilience against cyberattacks - is not a one-time project. It requires regular questioning, assessment, review, and monitoring, as well as the continuous consideration of new threats, including adjustments to established procedures and practices.
Implementing NIS2 is challenging, but manageable. With a clear roadmap, appropriate methods and tools, as well as the support of experienced partners, compliance can be achieved in a structured, efficient, and sustainable manner.
Achieve your NIS‑2 compliance — structured, prioritized, and practical in 5 steps.

Trainee Information Security Consultant
Both during his studies and bachelor thesis and his time at HvS, he engaged intensively with the NIS2 Directive and developed profound expert knowledge. A key outcome of his work was the development of a self-assessment tool to determine the NIS2 maturity level of organisations. His goal is to convey complex regulatory requirements in a clear and practical manner.