
How Shai-Hulud Recently Compromised Over 750 npm Packages
How Shai-Hulud Recently Compromised Over 750 npm Packages

High-profile supply chain attacks such as the insertion of a backdoor into SolarWinds in 2020 or the near-global compromise of OpenSSH server software via a backdoor in XZ Utils in 2024 attracted international attention. Companies mostly responded with short-term measures. As serious as these cases are, they often divert attention from the actual risk: everyday but frequently overlooked supply chain attacks on software libraries and software dependencies.
Attacks against the Node Package Manager (npm) – the standard package manager of the JavaScript runtime environment Node.js – in recent weeks have clearly highlighted the current threat landscape:
Although GitHub, Inc., the parent company of npm, has already announced extensive security measures for the Node Package Manager, organisations are still required to take action themselves: by consistently applying measures from the secure software development lifecycle (SSDLC) in order to independently increase their resilience against supply chain attacks.
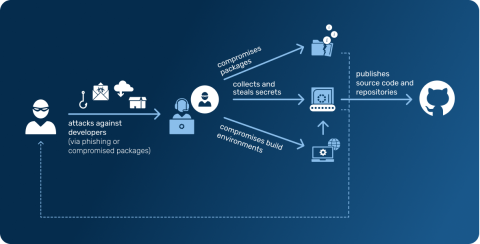
The risk potential of compromised software dependencies becomes particularly evident in successful attacks on continuous integration and continuous deployment (CI/CD) environments.
A striking example is the Shai-Hulud attack: this worm collected secrets from short-lived build and development systems and used them immediately to unauthorisedly publish infected updates of other npm packages maintained by the same maintainer.
The stolen credentials were additionally exfiltrated into specially created GitHub repositories named
In our threat notifications, we documented the observed attack mechanisms. This enables organisations to identify risks at an early stage and derive appropriate measures to secure dependencies, CI/CD pipelines and secrets management.
Worm-like attacks on software dependencies allow attackers to infect hundreds or even thousands of systems unnoticed with a single, targeted attack – (unfortunately) extremely efficiently.
In modern CI/CD environments, short-lived containers dominate, as do lightly monitored cloud components. This makes timely detection and appropriate response nearly impossible.
Such attacks regularly lead to the exfiltration of sensitive assets, such as valuable secrets, credentials, and source code, which can then be used for post-exploitation and persistence of the attack.
We recommend implementing the following best practices from the secure software development lifecycle (SSDLC) to effectively reduce vulnerability to supply chain attacks on software dependencies:
npm ci instead of npm install, --ignore-scripts, perform regular npm audit scans, and consider pnpm for better isolation.Threat modelling, dependency tracking, patch management, logging… all key elements of secure software development and absolutely essential for managing supply chain attacks. Our Cyber Security LABs for developers teach exactly these aspects in a practical and targeted way.
It can be expected that the simplicity and effectiveness demonstrated by Shai-Hulud will serve as a blueprint for future supply chain attacks using worm-like malware.
The impact achieved has vividly shown various stakeholders the inherent vulnerabilities that modern software development entails under the paradigm of CI/CD.
In addition to the global security measures implemented by the companies behind the registries, it is essential to act proactively and embed your own security measures early in the software development process.
Prevention, monitoring, and security awareness are crucial to detect compromised software dependencies early and either prevent damage entirely or at least limit it effectively.
With our Threat Insights, you receive timely information on relevant cyber risks, IOCs, threat-hunting rules, and actionable recommendations – try it free for 30 days.

Co-Head of Incident Response at HvS Consulting
He has extensive experience in incident response and digital forensics with DAX-30 and FTSE-500 companies. Marc is at home in two worlds – offensive security and incident response: while he focuses on analysing and resolving security incidents in his daily work, he does not hesitate to use hacking tools himself during purple-teaming exercises.