
EU Cybersecurity Regulation
EU Cybersecurity Regulation

With the implementation of the NIS-2 directive, the EU is significantly tightening cybersecurity requirements. Even though the national implementation in Germany only took place in December 2025, many companies already face the need to take action.
Companies that fall under the scope of the directive must implement comprehensive security measures and can expect significant sanctions in case of violations. This article explains the requirements set by the NIS-2 directive, who is affected, and how it differs from KRITIS, ISO 27001, and TISAX®.
The NIS-2 directive establishes uniform minimum requirements for cybersecurity across the EU. The aim of the NIS-2 regulation is to enable companies and organizations to detect cyberattacks early, assess them in a structured way, and respond effectively.
The introduction of NIS-2 is a direct response to the massive changes in the digital landscape since 2016, the year of the original NIS directive. Today, digital infrastructures are significantly more complex, highly interconnected, and interdependent. At the same time, the threat landscape has intensified: cyberattacks have become more professional, faster, and more frequent.
A security incident is no longer limited to a single company. Outages or disruptions can affect entire supply chains, disable critical services, and cause significant economic damage even across national borders.
With NIS-2, the EU aims to achieve a consistently higher and comparable level of security in all member states. The directive requires affected organizations to systematically identify, understand, and assess cyber risks and to implement appropriate technical and organizational measures.
Cybersecurity is thus explicitly established as a management and strategic issue. It is no longer merely a technical discipline but a central factor for the stability, trust, and competitiveness of the European economy.
According to Bundesamt für Sicherheit in der Informationstechnik (BSI) estimates, around 29,000 companies in Germany are affected.
Whether a company falls under the NIS 2 Directive essentially depends on two criteria:
NIS 2 divides affected companies into:
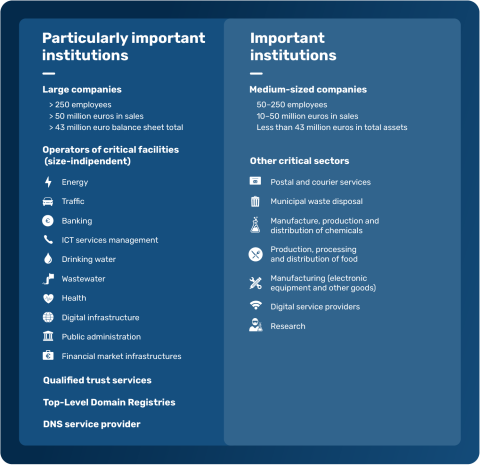
Particularly important entities (PIEs) are primarily large companies that provide services in one or more particularly important sectors. The following thresholds apply:
Size-dependent
Companies with more than 250 employees or annual revenue > €50 million and a balance sheet total > €43 million that operate in a particularly important sector (sectors of particularly important entities under the NISUmsuCG).
Size-independent
Important entities (IEs) are primarily medium-sized companies that provide services in one or more important sectors. However, there are also exceptions:
Size-dependent
Companies with more than 50 employees or annual revenue > €10 million and a balance sheet total > €10 million that operate in a particularly important or important sector (sectors of particularly important and important entities under the NISUmsuCG).
Size-independent
In addition, trust service providers (TSPs), providers of publicly available telecommunications services, or operators of public telecommunications networks qualify as IEs even if the criteria for size or revenue are not met.
With the NIS 2 Directive, many companies are asking how it relates to existing regulations and standards. In particular, comparisons with KRITIS requirements or established standards such as ISO/IEC 27001 are obvious.
Although the regulations partly overlap in terms of content, they pursue different objectives, address different target groups, and have different legal effects. A clear distinction is therefore essential in order to correctly classify obligations and avoid duplicate work or incorrect assumptions.
Until now, IT security requirements for KRITIS operators have been regulated exclusively by national law, particularly § 8a BSIG. With NIS 2, this framework is expanded at the EU level: KRITIS companies are now considered particularly important entities and are additionally subject to extended governance, reporting, and management requirements.
The good news for many companies:
Companies that already operate an information security management system (ISMS) in accordance with ISO/IEC 27001 have already fulfilled a key requirement of the NIS 2 Directive: the structured and continuous management of information security. The fundamental requirements for risk analysis, deriving measures, documentation, and continuous improvement are therefore largely covered.
The situation is similar with TISAX®. Organizations that have established an ISMS based on the VDA ISA also meet the NIS 2 requirements. A detailed statement on this was published by the ENX Association.
Long story short: a TISAX® assessment (at assessment level 3) largely fulfills the requirements of NIS 2.
Regardless of whether an ISMS based on ISO/IEC 27001 or TISAX has already been implemented:
NIS 2 introduces additional formal obligations that are not fully covered by existing standards. These include, in particular, governance, documentation, and reporting obligations that must be specifically supplemented.
How HvS-Consulting can support you:
Do you already have an ISMS based on ISO/IEC 27001 or TISAX and want to close the gaps to NIS 2? We would be happy to advise you.
In addition to technical and organizational security measures, the NIS 2 Directive also introduces a number of formal obligations. These primarily concern reporting, documentation, and governance requirements and go beyond what many companies already know from ISO/IEC 27001 or TISAX. The key aspect is less the creation of new security structures than their formal integration, documentation, and timely implementation in accordance with legal requirements.
NIS 2 requires affected companies to register within three months after the law enters into force. Since the law was adopted on December 6, 2025, registration must therefore be completed no later than March 5, 2026.
Both particularly important entities and important entities must register via the reporting and information portal.
In the event of significant security incidents - incidents that noticeably impair the availability, integrity, confidentiality, or authenticity of network and information systems or endanger the operation of essential services - both particularly important entities (PIEs) and important entities (IEs) must comply with staggered reporting obligations.
If there is suspicion of unlawful or malicious activities, an early initial notification must be submitted within 24 hours. This serves rapid situational assessment and early warning.
Regardless of an early initial notification, a significant security incident must be reported within 72 hours at the latest. This report should include, in particular, information about the severity and the impact of the incident.
The Bundesamt für Sicherheit in der Informationstechnik may request an interim report containing an updated assessment of the incident and the current status of handling. An interim report is not required automatically but only upon explicit request.
If a security incident lasts longer than one month, a progress report is required. This report provides information on the current status, remaining risks, and further measures.
Once the incident has been resolved, a final report must be submitted. It must include information on:
The Bundesamt für Sicherheit in der Informationstechnik has announced that the reporting portal will be activated by January 6, 2026.
In the event of a significant security incident, the Bundesamt für Sicherheit in der Informationstechnik may order affected companies to inform their customers without delay. The purpose of this obligation is to create transparency, limit potential consequential damage, and enable those affected to take appropriate protective measures.
Within the framework of NIS 2 evidence obligations, a distinction must be made between the following groups:
For KRITIS operators, stricter requirements apply to the implementation of security measures. At the same time, they are required to regularly and proactively demonstrate compliance with these requirements to the competent authority.
The evidence must be submitted every three years and must be provided by a suitable auditing body.
How HvS-Consulting can support you:
HvS-Consulting is considered a suitable auditing body for audits in accordance with § 8a BSIG (KRITIS audits).
Further information can be found here.
Particularly important institutions and important institutions that are not KRITIS operators are also subject to evidence obligations. However, unlike KRITIS operators, they are not required to submit evidence proactively.
Instead, the Bundesamt für Sicherheit in der Informationstechnik may request evidence to assess NIS 2 compliance as part of its supervisory activities, for example:
In addition, the BSI is authorized to conduct its own audits and inspections or to commission third parties to do so. If deficiencies are identified, the BSI may order the remediation of the identified shortcomings.
Against this background, it is advisable not to wait for an official request but to implement the NIS 2 requirements in a structured manner at an early stage and maintain appropriate documentation.
In addition to the formal obligations, companies must implement extensive security measures.
The NIS 2 Directive marks a significant turning point for cybersecurity in Europe. With the entry into force of the German implementation act, affected companies are now required to address the requirements in a concrete and binding manner.
For many companies, particularly in the German SME sector, this means:
The phase of uncertainty is over. NIS 2 is no longer an abstract EU initiative, but applicable law with concrete obligations.
In another blog article, we show how NIS 2 can be implemented in a practical and resource-efficient way.
There, we move beyond the legal perspective and focus on concrete implementation. Among other things, you will learn:
Read the next article: “NIS2 implementation: a practical guide to achieving regulatory compliance [incl. checklist].”

Trainee Information Security Consultant
Both during his studies and his bachelor’s thesis, as well as during his time at HvS, he has worked extensively on the NIS 2 Directive and built solid subject-matter expertise. A key outcome of his work was the development of a self-assessment tool to determine the NIS 2 maturity level of organizations. His goal is to make complex regulatory requirements understandable and practical.
Head of Information Security at HvS-Consulting
Our specialist for ISMS. He knows what makes an ISMS successful, how it can be developed securely and according to organizational needs, and above all how to make it resilient. He explains which processes and policies need to be established in your organization.
