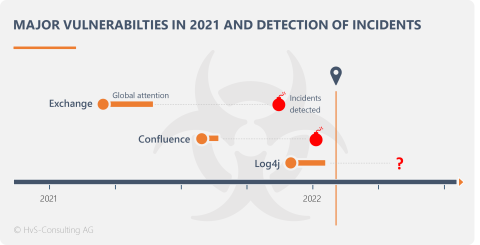
ProxyLogon in Exchange, OGNL injection in Confluence, log4shell in the log4j library. 2021 was rife with critical vulnerabilities. They were exploited by ransomware gangs and hackers for mining crypto currencies. But where have the professional spies, the APT groups been? Did they miss such opportunities and take a vacation from cyber warfare? Surely they didn't. And we have collected evidence.
Download Threat Report Emissary Panda
The benefactors of the scatter fire
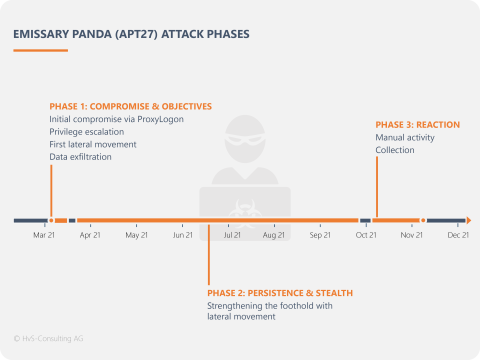
The APT group Emissary Panda (also known as APT27, LuckyMouse) has exploited the Microsoft Exchange vulnerability "ProxyLogon", often publicly referred to as "Hafnium" vulnerability, to carry out targeted industrial espionage. The particularly perfidious aspect of this is that they intentionally acted like "ordinary hackers" in order to not trigger a comprehensive analysis and remediation. With great success.
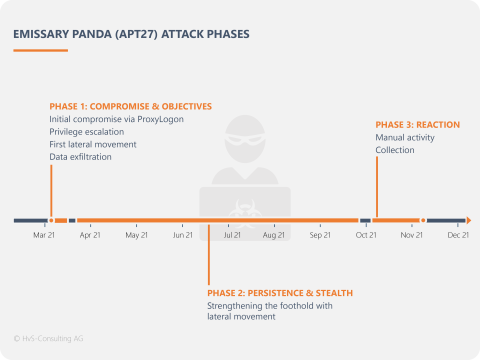
We analyzed several incidents and found that some customers did not seriously follow up on a ProxyLogon compromise because at first glance it looked like an attack by an occasional attacker. This is how Emissary Panda (APT27) managed to run through the classic APT kill chain and steal trade secrets undetected for months.
Our report not only provides background and details on the process, the TTPs and the IOCs, but also initial evidence that the OGNL injection in Confluence was and is also being of interest for targeted industrial espionage. The same applies for log4shell.
The PDF is written for security experts. However, the findings are also and especially important for decision-makers in companies and are therefore summarized on this page.
Strategies for Cyber Security 2022
The effects of the global vulnerabilities from 2021 will only gradually come to light... or as a German soccer manager once so aptly put it: "Only when the snow melts you will see where the poo is".
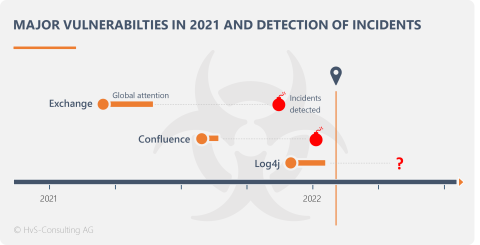
We have to assume that numerous APT and other compromises by ProxyLogon (Exchange), OGNL injection (Confluence) and log4shell (Log4j) are still undetected. Especially for log4shell, the typical detection period of 3 - 6 months has not even been reached yet.
In addition, global vulnerabilities will again come to light and be exploited in 2022. Anything else would be close to a miracle. Companies are therefore well advised to prepare for this. We have the following recommendations based on our experience and findings:
Prediction
Get in front of the wave
- Subscribe to advisory feeds
The clock starts ticking when the security alert is published. When you first learn about vulnerabilities from authorities or newspapers, it is often already too late. - Asset management rules! Take care of your CMDB
Only if you really know your systems you can find out fast enough if and where you are affected by a vulnerability. - Take any compromise seriously
Our analyses prove that APT groups disguise themselves as "hackers from the masses" and also sometimes leave a cryptominer as a honeypot for forensic experts, hoping that the case will then not be investigated further and affected systems will not be rebuilt.
Protection
Do not sit out, but act
- Patch critical vulnerabilities immediately
All major vulnerabilities from 2021 were exploited within hours. A "I patch once a month" process is lethal for such critical events. - Create a plan B like BCM
Sometimes patches are not available at all or cannot be applied immediately for certain reasons. In that case, you should provide additional protection for affected services or temporarily deactivate them. But to do this, you need to understand the business impact. And this is where BCM starts. Which services are critical to your business and what would a temporary loss imply? - Readiness saves time and money
A disproportionately large number of attacks start at the weekend. Why? Hackers don't care about weekends and holidays, they take advantage of them! That's why a functioning emergency team should also be able to respond on weekends, and not just in IT, but also in management. Serious decisions must also be made at 3 a.m. on Saturday morning. An investment that pays for itself very quickly in an emergency. - Every critical vulnerability is equally important
We can really understand statements like "I can't keep patching Exchange", we are also sometimes tired of incidents. But this is comparable to an antelope escaping the first lion and saying, exhausted, to the second lion: "Hey, I can't run again".
Detection/Response
The next vulnerability is coming for sure
- Only pros help against pros
Detecting non-obvious vulnerabilities and professional attacks is anything but trivial. Secure appropriate skills, either in your own CDC or through contracts with service providers. There are way too few incident response professionals for "wildfires" like Hafnium or Log4j. - The mean time to detect (MTD) must be reduced
Nowadays, an infected endpoint device should not kill you. Full stop. "Assume compromise" has been the security motto for years. The "break of the neck" usually occurs after about 2 weeks (APT ransomware) to 6 months (APT espionage). If a compromise is discovered within a week, the chances of getting off lightly are good. - Thinking outside the box
Do not focus only on the infected system. After all, that is usually only the entry point. Every investigation requires criminal intuition. What credentials could the attacker capture? Where can he go with them? Which systems are accessible at all? Are there comparable IOCs on these?
Download Threat Report Emissary Panda