500+ Kunden schenken uns ihr Vertrauen, von Startups bis zu Großunternehmen
Your 1. problem
You have been hacked! Possibly also encrypted and extorted. And you don't know how the attackers actually did it, nor how to react properly, nor how to get rid of the invaders.
Your 2. problem
Completely exceptional situation: Everyone tries to react, but everyone does something, uncoordinated, sometimes even wrong. You lose a lot of money every day due to wrong decisions.
Our solution
Our incident response experts manage emergencies professionally and efficiently, from technical control and forensics to crisis communication and remediation.
Have you been attacked?
You are not looking for information but for help in an immediate emergency? Please contact our Incident Response hotline at
or by e-mail at:
incidentresponse@hvs-consulting.de
or use our contact form:
The right response for your incident
A cyber incident is an absolutely exceptional situation. Most of the people affected are experiencing such an emergency for the first time and usually have neither plans nor instructions or processes to master this situation.
Yet incident response is much more than forensic analyses and the implementation of individual technical measures. It requires up-to-date situation reports, structures and, above all, a professional incident coordinator who manages the parties involved (IT, management, forensic experts, PR, etc.), brings calm and structure to the usually uncoordinated actionism, and defines and pursues clear investigative goals in order to end the emergency situation quickly and cost-effectively.
Our experts have mastered hundreds of incident response missions over the last 10 years, from medium-sized businesses to large corporations (DAX40) and have built up a wealth of experience. In times of peace we support you in optimizing your cyber defense and in case of emergency with coordination, forensic analysis and internal and external communication.
Incident Response supports you during a security incident – but what if you could identify risks earlier?
With HvS Threat Insights, you stay informed about current threats and identify relevant risks before they become a security incident.
Forensic analysis of the affected systems provides us with valuable information about the attack. How did the attackers act? Which Tactics, Techniques and Procedures (TTPs) did they use? What Indicators of Compromise (IoCs) did they leave behind to help us identify compromised assets? What is the entry vector and what vulnerabilities were exploited that need to be fixed to avoid a recurrence of the incident? The information collected during the analysis can ultimately provide information about the damage caused and the motive of the attackers, and sometimes even allow attribution to a known group of perpetrators. Depending on the number of systems, the urgency and the desired depth of analysis, we use different approaches:
Triage
First, we analyze potentially affected systems - like triage in medicine - with a reduced but appropriate scope. We collect and analyze only certain artifacts from each suspicious system. This approach is of course less accurate than a full forensic analysis, but provides enough material for further decisions and saves tremendous time, money and effort. On this basis, we plan and prioritize the appropriate further steps.
Detailed analyses
The "classic" form of forensic analysis. We analyze an identical copy of a data carrier using modern forensic programs and techniques. This analysis technique often provides detailed results, but is very time consuming. Additionally, a RAM dump of a running system can be analyzed to examine volatile information such as running processes and open connections of the target system. This is important to understand the attackers' approach.
Area analysis
In some incidents, a large number of systems are potentially affected, several hundred or even a thousand. Often, there is initially no evidence of the original entry vector (the "patient zero") or a domain controller is compromised and thus no system can be excluded. In these cases, we perform area-wide analyses regarding the known traces of the attack, in a compromise assessment with our IOC Scanner Thor.
If there are any anomalies in the area-wide analysis, triage is again initiated and the various phases are iterated until no new findings emerge.
The results of the various analysis approaches are consolidated into a timeline and further analyzed to correlate attacker activity across multiple systems and identify interactions between them. We classify the steps/phases of the attack based on the MITRE ATT&CK framework. This helps to identify the attacker's approach and motive, as well as take remedial actions and prevent such attacks in the future.
Do you want to react professionally in the event of an emergency?
Let's get to know each other in a web meeting and talk about possible approaches.
What systems can we analyze
Windows
Since most organizations run a Microsoft environment, Windows systems (servers & clients) are also the most commonly analyzed. We use specialized tools for evidence collection and forensic analysis.
Linux
Although incidents occur more frequently on Windows systems, we can also perform forensic analysis of Linux systems and have the appropriate specialized tools and know-how.
Mac
Even if Macs are still rather exotic in enterprises they are also compromised and therefore we can do forensic analysis of Apple systems as well.
Cloud Assets
Since cloud environments are very different from on-premise environments, they also require different approaches and methods for incident response. Our team has handled a wide variety of cloud incidents in Azure and AWS Cloud.
Endpoint Detection and Response (EDR)
To be honest, we prefer an analysis of your infrastructure via EDR solutions. Why? The central management allows us to quickly collect artifacts for further analysis, the telemetry data often reveals the exact actions of the attackers, and we can quickly implement effective monitoring for further activities.
Log data
Log data in particular from central systems also help with the analysis once the initial facts are known. This allows suspicions to be quickly narrowed down, ruled out or corroborated. In addition, centrally stored log data is difficult for attackers to manipulate.
The final goal of any incident response is to regain sovereign control over the IT infrastructure, prevent the reoccurrence of a similar attack, and remove all traces on the systems to restore a clean baseline.
Typical actions include rebuilding compromised systems and changing all passwords on compromised accounts. All of this should take place in a short period of time, usually within a day, so that attackers have as little chance as possible to recompromise systems that have already been rebuilt.
This is usually hard work and requires many people to be involved, right up to the top management level, as in most cases such a "D-Day" will have an impact on business operations. In addition, you absolutely need professional project managers who can create a clean and realistic schedule, assign roles and responsibilities, ensure communication between stakeholders, and keep quality under control using KPIs.
More Incident Response topics

Security incident in M365? Our Incident Response Team helps you to quickly contain and eliminate threats - for minimum downtime and maximum security.
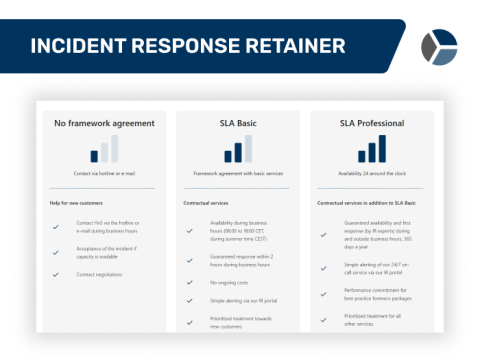
In an IT emergency, every second counts - our incident response experts are on hand 24/7 to provide you with professional assistance. With a framework agreement, you have prioritized treatment compared to new customers.
IT incident? Ransomware? Hacking? As experts in incident management and incident response, we are at your side.
Get in touch with us!

Find hacker activity before it's too late - with proactive threat hunting and compromise assessments.

Successfully build & optimize your Cyber Defense Center! We work with you to develop a customized CDC strategy, improve detection & response and set clear priorities for greater security.