
17 study interviews with SMEs: a clear pattern
17 study interviews with SMEs: a clear pattern

"NIS-2 applies – but many small and medium-sized enterprises (SMEs) don’t know whether they are affected."
This concise insight was summed up by our colleague Younes Ahmadzei when he presented the results of his bachelor’s thesis at BSides Munich. In 17 interviews with CEOs, IT managers, and CISOs of non-CRITIS SMEs, a clear picture emerged:
NIS-2 has arrived, but implementation is stalling.
Many mid-sized companies objectively fall within the scope of the NIS-2 Directive – yet few are aware of it. The interviews revealed three key causes:
„Honestly, I don’t understand any of it. It’s all such a mess of terms."
The interviews revealed four structural challenges that particularly affect mid-sized companies:
„At least one person, two to three days a week, just for this topic.“
These hurdles explain why NIS-2 is acknowledged but hardly actively addressed.
The extent of uncertainty and reluctance in mid-sized companies became strikingly clear during the data collection for the study. From an initial list of 3,000 companies, 1,800 were identified as potentially falling under NIS-2. Despite sending around 3,600 emails, only 17 interviews were ultimately conducted.
Many organizations declined, citing:
This response rate alone shows that mid-sized companies are aware of NIS-2 – but do not feel capable of engaging with it.
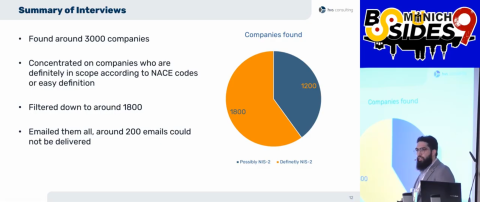
Source: BSidesMunich
Many initially think of NIS-2 as purely a “compliance issue.” However, the interviews show that the challenges run deeper:
Classification problem
Many companies responded to inquiries with confusion, claiming the law did not yet apply or that they were not affected, even though they fall within the scope based on objective criteria (sector and size).
Implementation problem
Even when the intent is there, practical implementation often fails due to the complex governance and documentation requirements, which seem designed more for large corporations than for SMEs.
The real risk, therefore, lies not just in potential sanctions, but in the structural postponement of security-relevant measures. Many of the elements required by NIS-2, such as:
are not just formal requirements, but essential building blocks of modern IT security. Waiting here delays not only compliance but also cyber resilience.
For many SMEs, NIS-2 is not an isolated regulatory issue – it is becoming a market factor:
Companies that do not address NIS-2 today risk not only regulatory uncertainty but also long-term competitive disadvantages.
The interviews revealed a frequent gap between technical security and formal compliance:
"Operationally, we are well prepared. Organizationally and in terms of documentation [...] we are not there yet."
"The step from TISAX® to NIS-2 is very small – the structures are already in place."
These examples show: those who view NIS-2 not as an isolated requirement but as part of a broader security strategy (e.g., aligned with ISO 27001 or TISAX®) can leverage synergies – and avoid duplicate efforts.
The interviews clearly show: SMEs need structure, guidance, and translation.
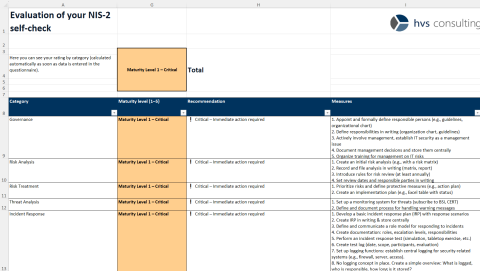
As part of the bachelor’s thesis, an Excel-based self-assessment tool was developed.
This tool helps companies to:
NIS-2 is more than a bureaucratic hurdle or an isolated piece of legislation. The directive provides a framework for structuring cyber resilience in SMEs – and creates an opportunity to critically assess one’s own security organization. Companies that evaluate early on to what extent they are affected and use established standards as guidance gain a clear advantage: legally, organizationally, and in terms of security.
The real question, therefore, is not whether NIS-2 creates effort – but whether further delay is sustainable in the long run.
The directive provides a framework for strengthening cyber resilience in SMEs – and offers an opportunity to critically assess their security posture.

Trainee Information Security Consultant
Both during his studies and bachelor’s thesis, as well as in his time at HvS, he has worked extensively on the NIS-2 Directive and built solid expertise in the field. A key outcome of his work was the development of a self-assessment tool to determine the NIS-2 maturity level of organizations. His goal is to make complex regulatory requirements understandable and practical.